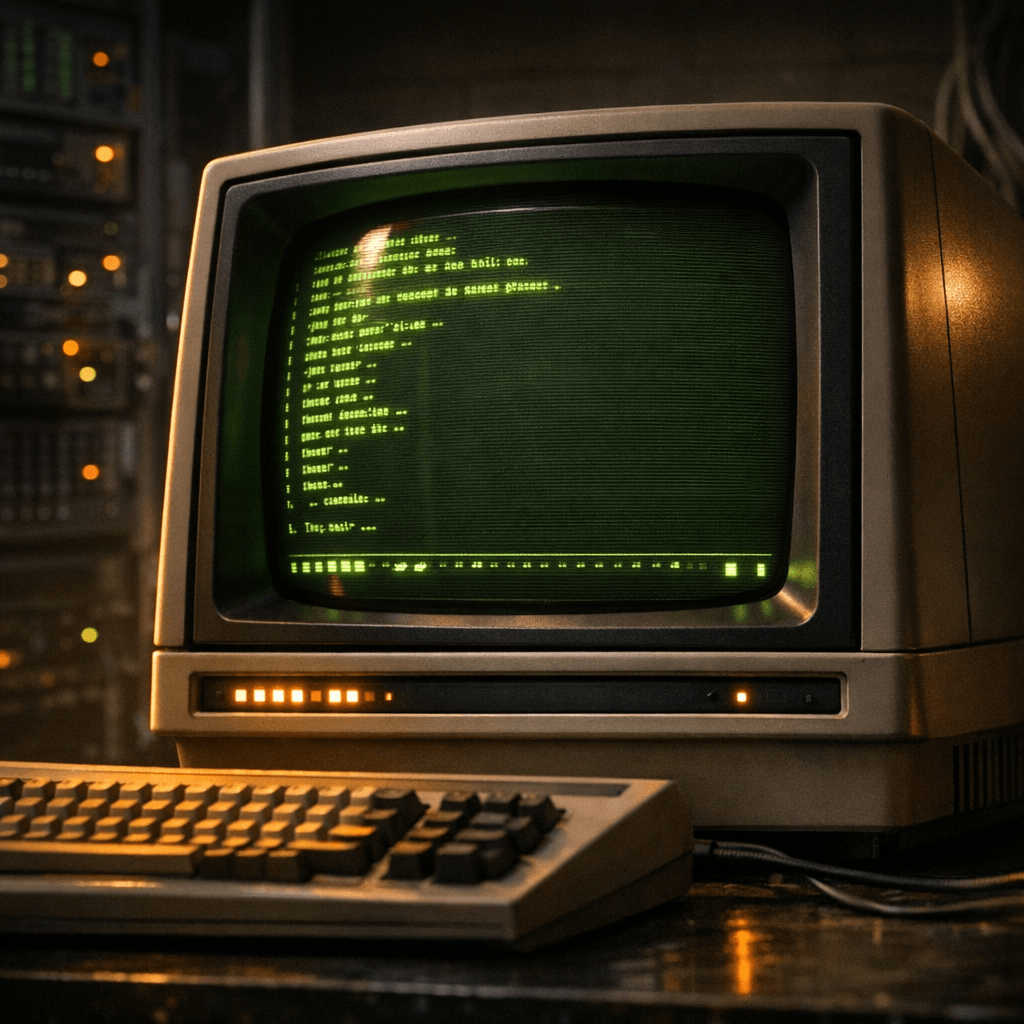
Classic MUDs with Telnet clients
Historical MUD research requires more than nostalgia. This guide provides concrete procedures for authenticating vintage servers, capturing byte-perfect session data, and submitting findings to preservation archives. Methods focus on terminal emulation accuracy, DNS archaeology, and standardized logging formats essential for academic and hobbyist preservation projects.
Verify Server Provenance Against Primary Sources
Cross-reference the server's claimed lineage against the original DikuMUD source releases mirrored on GitHub (https://github.com/dikuMUD) and the Stanford University MUD history timeline. Check compilation dates in the original Makefile or CHANGELOG files against the server's advertised founding date to confirm authenticity.
⚠ Common Pitfalls
- •Accepting Wikipedia edit timestamps as server founding dates
- •Confusing derivative codebases (CircleMUD, ROM) with original DikuMUD instances
Configure Terminal Emulation for Authentic Rendering
Historical MUDs expect CP437 or ISO-8859-1 character sets with VT100 control sequences. Set your terminal to DEC VT100 mode to ensure ANSI color codes and line-drawing characters render identically to 1980s hardware, preventing parser errors in menu systems.
TERM=vt100 LANG=en_US.ISO-8859-1 telnet mume.org 4242⚠ Common Pitfalls
- •Using UTF-8 locales which mangle box-drawing characters
- •Enabling modern terminal features (mouse, 256-color) that confuse legacy parsers
Capture Byte-Perfect Session Logs with Timing Data
Use ttyrec or script -t to record timing data alongside output. This preserves the temporal dimension of gameplay critical for understanding pacing and latency in early netcode, and captures raw ANSI escape sequences that plain text copy-paste destroys.
ttyrec -e "telnet mud.dum.ac.uk 27723" session_$(date +%Y%m%d).ttyResolve Historical DNS via Archive Snapshots
Many classic MUDs moved between hosts or lost original domains. Query the Wayback Machine's historical URL availability API or securitytrails.com for historical A records and NS delegations from the 1990s to locate original IP ranges even if current DNS is parked or redirected.
⚠ Common Pitfalls
- •Assuming current DNS A records match 1990s hosting
- •Ignoring historical subdomain conventions (mud.host.edu versus host.edu)
Document Telnet Handshake Negotiation
Log the initial IAC (Interpret As Command) sequences for terminal type (TTYPE) and window size (NAWS). These reveal how the MUD engine detected client capabilities and adjusted pager behavior, line wrapping, and prompt rendering in real-time.
telnet -E -t vt100 mume.org 4242 2>&1 | tee raw_negotiation.txtCross-Reference with Contemporary Directories
Validate current operational status against mudstats.com and mudconnect.com. These directories preserve metadata fields including base codebase, last verified online timestamp, and original author credits that distinguish original instances from later reconstructions or derivatives.
⚠ Common Pitfalls
- •Trusting DNS SOA dates as uptime proof
- •Confusing open ports with active game worlds
Normalize Logs for Archival Submission
Convert proprietary ttyrec or script outputs to standardized formats for submission. Extract plain text with ttyplay -p for fulltext indexing, or use ansi2html to create web-viewable artifacts. Submit packages to the Internet Archive with metadata tags including classic-mud, telnet-archive, and specific codebase identifiers (e.g., diku, lp, tiny).
ttyplay -p session.tty 2>/dev/null | cat -v > session_plain.txtWhat you built
Archival work requires rigorous chain of custody from connection to publication. Always retain original binary captures alongside normalized formats to preserve both authenticity and accessibility. Submit session logs with structured metadata including connection date, terminal type negotiated, and observed codebase characteristics to enable future researchers to verify your findings against primary sources.